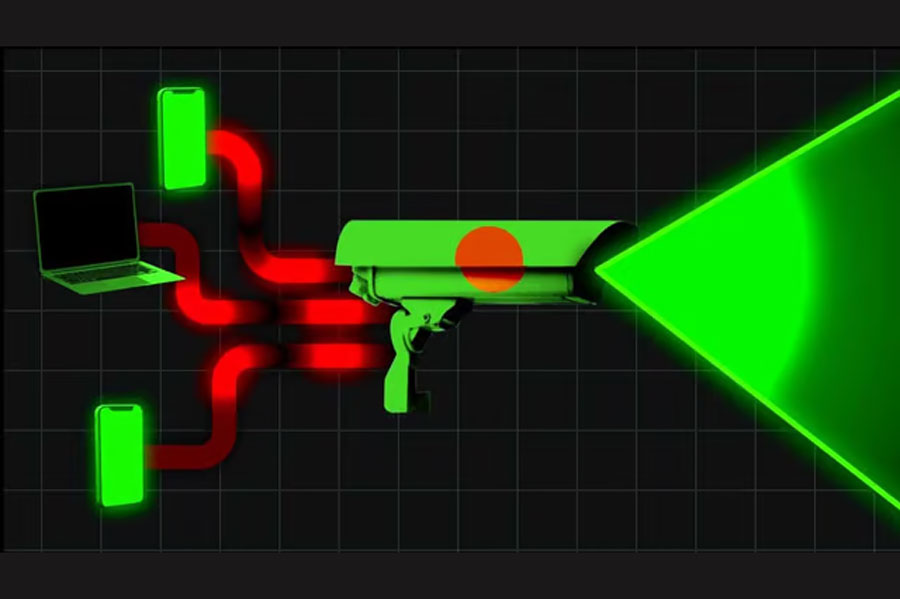
NTMC database exposed personal info to open web: report
Major General Ziaul Ahsan, director general of NTMC, says information about the data leak is ‘totally incorrect’
Published :
Updated :
The National Telecommunication Monitoring Centre (NTMC) in Bangladesh has exposed a database to the open web. The types of data that leaked online were extensive, American technology magazine WIRED reports.
The list of data is long: names, professions, blood groups, parents’ names, phone numbers, the length of calls, vehicle registrations, passport details and fingerprint photos, according to the report.
When asked by bdnews24.com, Major General Ziaul Ahsan, director general of NTMC, said the information about the data leak was “totally incorrect”.
These are sample data which are always collected for research and development, he said. “These are not original data.”
WIRED reported that it was not a typical database leak. For months, NTMC published people’s personal information through an “unsecured” database linked to its systems. And this past week, anonymous hackers attacked the exposed database, wiping details from the system and claiming to have stolen the trove of information, according to the report.
WIRED said it verified a sample of real-world names, phone numbers, email addresses, locations, and exam results included in the data. However, the exact nature and purpose of the amassed information is unclear, with some entries appearing to be test information, incorrect, or partial records.
The disclosure, which appeared to be unintentional, provided a tiny glimpse into the highly secretive world of signals intelligence and how communications may be intercepted.
“I wouldn’t be expecting this to happen for any intelligence service, even if it’s not really something that sensitive,” said Viktor Markopoulos, a security researcher for CloudDefense.AI who discovered the unsecured database. “Even if many data are test data, they still reveal the structure that they’re using, or what exactly it is that they are intercepting or plan to intercept.”
The vast majority of the data exposed in the NTMC database is metadata—the extremely powerful “who, what, how, and when” of everyone’s communications. Phone call audio was not exposed, but metadata shows which numbers may have called others and how long each call lasted.
This kind of metadata can be used broadly to show patterns in people’s behaviour and whom they interact with.


 For all latest news, follow The Financial Express Google News channel.
For all latest news, follow The Financial Express Google News channel.